In an increasingly digital world, businesses can no longer afford to treat technology as a secondary function. Instead, IT must…
Author: admin
How IT Consultants Help Build Data-Driven Organizations
In today’s digital economy, data is no longer just a byproduct of business operations—it is the foundation of competitive advantage….
Telehealth Ecosystem Strategy: Integrating remote care tools for modern clinics
The healthcare industry is undergoing a digital transformation, driven by the need for accessible, efficient, and patient-centric care. One of…
Supply Chain Cyber Risk: Vetting the security of third-party software vendors.
In today’s interconnected digital ecosystem, organizations rarely operate in isolation. From cloud providers and SaaS platforms to outsourced development teams…
Serverless Architecture Advisory: Building Scalable Apps Without Managing Servers
As businesses strive to innovate faster and scale efficiently, traditional infrastructure models are increasingly becoming a bottleneck. Managing servers, provisioning…
PropTech Strategy: IT Consulting for Real Estate and Smart Building Management
The real estate industry is undergoing a significant transformation driven by digital innovation. Traditionally known for its reliance on physical…
Predictive Maintenance for Industrial IoT: Moving from reactive to proactive repairs
Industrial operations have long relied on maintenance strategies that are either reactive—fixing equipment after it fails—or preventive—servicing machines at scheduled…
Post-Quantum Cryptography: Preparing encryption for the era of quantum computing
The world of cybersecurity is built on trust—trust that sensitive data, financial transactions, and communications remain secure through encryption. For…
Multi-Cloud Networking: Ensuring seamless connectivity across AWS, Azure, and Google
As businesses continue their digital transformation journeys, cloud computing has become a cornerstone of modern IT infrastructure. Many organizations initially…
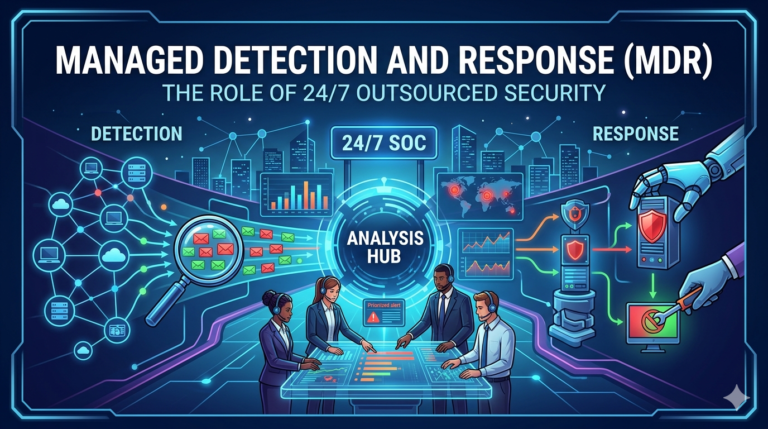
Managed Detection and Response (MDR): The role of 24/7 outsourced security
Cybersecurity threats have grown dramatically in both frequency and sophistication. Organizations today face constant risks from ransomware attacks, phishing campaigns,…