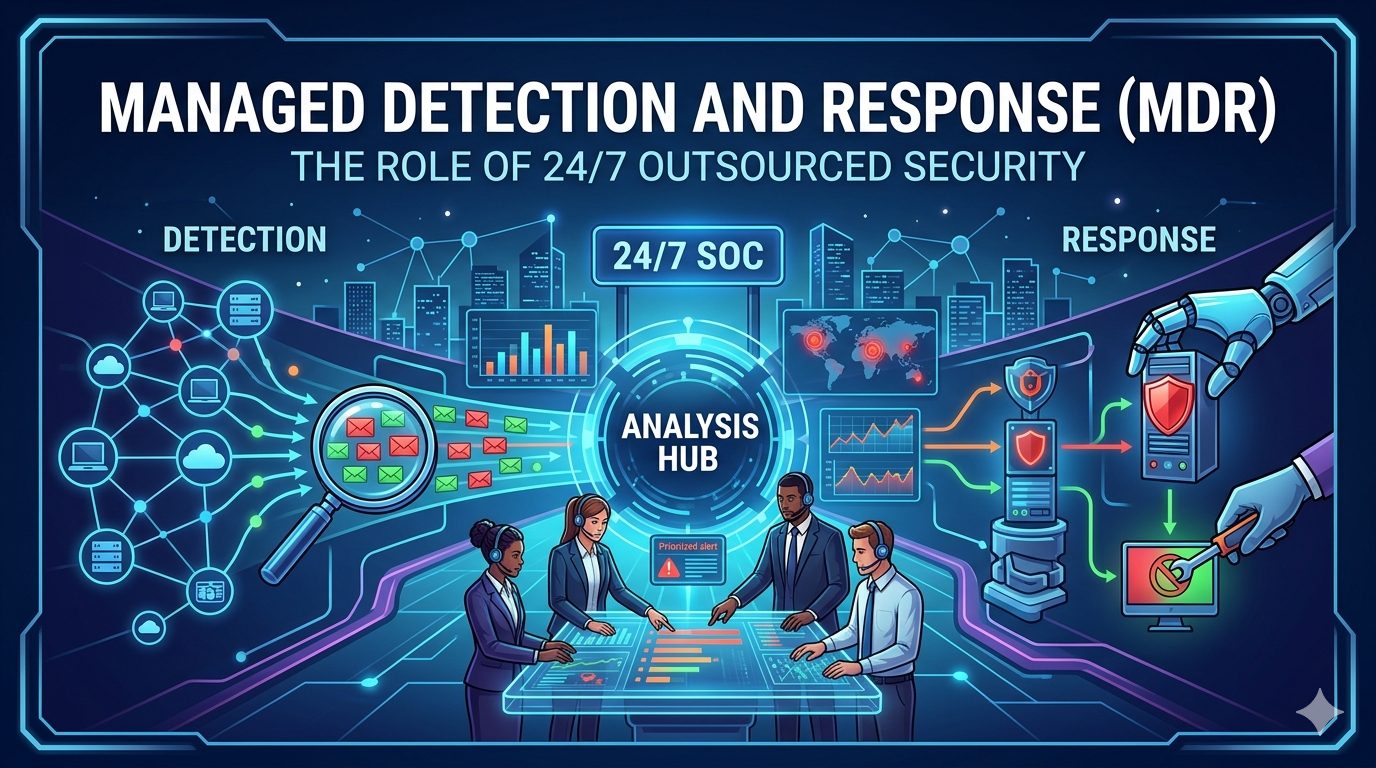
Managed Detection and Response (MDR): The role of 24/7 outsourced security
Cybersecurity threats have grown dramatically in both frequency and sophistication. Organizations today face constant risks from ransomware attacks, phishing campaigns, insider threats, and advanced persistent threats. While many businesses invest in firewalls, antivirus software, and monitoring tools, these technologies alone are not enough to defend against modern cyberattacks.
Effective cybersecurity requires continuous monitoring, rapid threat detection, and immediate response. However, maintaining a fully staffed, in-house security operations center (SOC) capable of monitoring systems around the clock can be expensive and difficult to manage—especially for small and mid-sized organizations.
This is where Managed Detection and Response (MDR) services play a crucial role. MDR provides organizations with outsourced cybersecurity experts who monitor networks, detect threats, investigate suspicious activity, and respond to incidents 24/7.
At CVDragon IT Consulting, we help businesses strengthen their cybersecurity posture through MDR solutions that combine advanced technology with expert threat intelligence. This article explores the importance of Managed Detection and Response and how it helps organizations stay ahead of evolving cyber threats.
Understanding Managed Detection and Response
Managed Detection and Response is a cybersecurity service that provides continuous monitoring, threat detection, and incident response through a team of external security professionals.
Unlike traditional security tools that simply generate alerts, MDR services actively analyze threats and take action to contain or eliminate them.
An MDR solution typically includes:
- Continuous network monitoring
- Threat detection using advanced analytics
- Security event investigation
- Incident response support
- Threat intelligence integration
- Security reporting and recommendations
In essence, MDR functions as an outsourced security operations center that operates around the clock to protect an organization’s digital environment.
Why Traditional Security Measures Are Not Enough
Many organizations rely primarily on preventive security tools such as firewalls and antivirus software. While these tools remain important, they are no longer sufficient to stop modern cyber threats.
Attackers now use advanced techniques that bypass traditional defenses, including:
- Zero-day vulnerabilities
- Fileless malware
- Social engineering attacks
- Credential theft
- Supply chain compromises
Even when security tools detect suspicious activity, organizations often lack the expertise or resources to analyze alerts quickly and respond effectively.
Without continuous monitoring and response capabilities, cyber incidents can remain undetected for weeks or months—giving attackers time to steal sensitive data or disrupt operations.
The Importance of 24/7 Security Monitoring
Cyber threats do not operate on business hours. Attackers often launch intrusions during nights, weekends, or holidays when internal security teams are less likely to notice unusual activity.
A 24/7 monitoring environment ensures that suspicious behavior is detected immediately.
Continuous monitoring enables organizations to:
- Identify security anomalies in real time
- Respond to incidents before damage escalates
- Reduce the time attackers remain inside systems
- Maintain visibility across all digital assets
MDR providers operate dedicated security operations centers staffed with analysts who investigate alerts and initiate response actions around the clock.
Key Components of MDR Services
Threat Detection
MDR platforms analyze security data from endpoints, networks, cloud environments, and applications. Advanced analytics and behavioral analysis identify suspicious activity that traditional tools may miss.
Threat Investigation
Security analysts examine alerts to determine whether they represent real threats or false positives. This reduces alert fatigue and ensures organizations focus on genuine risks.
Incident Response
When a threat is confirmed, MDR teams initiate response actions such as isolating compromised systems, blocking malicious IP addresses, or containing malware.
Threat Intelligence
MDR services integrate global threat intelligence data to identify emerging attack patterns and indicators of compromise.
Security Reporting
Organizations receive detailed reports outlining detected threats, response actions, and recommendations for improving security posture.
Benefits of Outsourced MDR Security
Access to Cybersecurity Expertise
Cybersecurity talent is in high demand, and many organizations struggle to hire experienced security professionals. MDR services provide access to skilled analysts without the cost of building a full internal team.
Continuous Protection
Round-the-clock monitoring ensures that threats are detected and addressed immediately, regardless of time or day.
Faster Incident Response
Quick response actions significantly reduce the impact of cyberattacks.
Reduced Operational Costs
Building and maintaining a 24/7 internal SOC requires significant investment in personnel, infrastructure, and technology. MDR provides enterprise-grade security capabilities at a predictable cost.
Improved Threat Visibility
Advanced analytics provide deeper insights into network behavior and potential vulnerabilities.
MDR vs. Traditional Managed Security Services
Managed Detection and Response differs from traditional managed security services in several ways.
Traditional managed security services typically focus on monitoring logs and generating alerts. However, they often leave investigation and response responsibilities to the client organization.
MDR goes further by:
- Investigating alerts in depth
- Providing threat hunting capabilities
- Actively responding to incidents
- Offering security expertise and guidance
This proactive approach enables organizations to address threats quickly and effectively.
MDR and Endpoint Security
Endpoints such as laptops, desktops, and mobile devices are common entry points for cyberattacks.
MDR solutions often integrate Endpoint Detection and Response (EDR) technologies that monitor device activity and detect suspicious behavior.
Capabilities include:
- Monitoring processes and system activity
- Identifying malicious software execution
- Isolating compromised devices
- Collecting forensic data for investigation
Combining EDR with MDR services strengthens overall endpoint protection.
MDR for Cloud and Hybrid Environments
As organizations move workloads to cloud platforms, security monitoring must extend beyond traditional networks.
MDR services provide visibility across:
- Cloud infrastructure
- Software-as-a-Service (SaaS) applications
- Hybrid IT environments
- Remote workforce devices
This ensures that security teams maintain comprehensive protection regardless of where data or applications reside.
Challenges Organizations Face Without MDR
Without continuous security monitoring, organizations often encounter several challenges:
- Delayed threat detection
- Limited visibility into network activity
- Overwhelming volumes of security alerts
- Insufficient incident response expertise
- Increased risk of data breaches
These challenges can result in severe financial losses, regulatory penalties, and reputational damage.
MDR services address these issues by providing both technology and expertise.
Best Practices for Implementing MDR
Organizations considering MDR adoption should follow several best practices:
- Conduct a cybersecurity risk assessment
- Identify critical systems and sensitive data
- Integrate MDR monitoring across endpoints, networks, and cloud platforms
- Establish clear incident response procedures
- Maintain communication between internal teams and MDR providers
- Continuously review security reports and recommendations
A collaborative approach ensures maximum value from MDR services.
The Future of Managed Security
As cyber threats continue to evolve, MDR solutions are incorporating advanced technologies such as artificial intelligence, machine learning, and automated threat response.
Future MDR capabilities may include:
- Predictive threat detection using AI
- Automated incident containment
- Advanced threat hunting using behavioral analytics
- Integration with broader security frameworks such as Zero Trust architectures
These innovations will further strengthen organizations’ ability to defend against sophisticated cyberattacks.
How CVDragon IT Consulting Supports MDR Implementation
CVDragon IT Consulting helps organizations implement and manage MDR solutions that provide comprehensive security protection.
Our services include:
- Cybersecurity risk assessments
- MDR strategy and implementation
- Endpoint and network monitoring integration
- Threat intelligence and analytics
- Incident response planning
- Continuous security optimization
By combining advanced technologies with expert security analysis, we help businesses build resilient cybersecurity environments.
Conclusion
Cybersecurity threats are becoming more advanced, persistent, and difficult to detect. Organizations can no longer rely solely on preventive tools or limited in-house monitoring capabilities.
Managed Detection and Response provides a powerful solution by delivering continuous monitoring, expert threat analysis, and rapid incident response through outsourced security operations.
By adopting MDR services, businesses gain the ability to detect threats faster, respond more effectively, and protect critical systems from cyberattacks around the clock.
At CVDragon IT Consulting, we empower organizations to strengthen their cybersecurity defenses with proactive MDR strategies—ensuring that security remains vigilant every hour of every day.



