Introduction: Sustainability Meets Digital Transformation Environmental, Social, and Governance (ESG) reporting has moved from being a voluntary initiative to a…
Category: Articles
EdTech Transformation: Navigating Digital Learning Platforms for Higher Education
Higher education is undergoing one of the most profound transformations in its history. The traditional classroom—once defined by chalkboards, lecture…
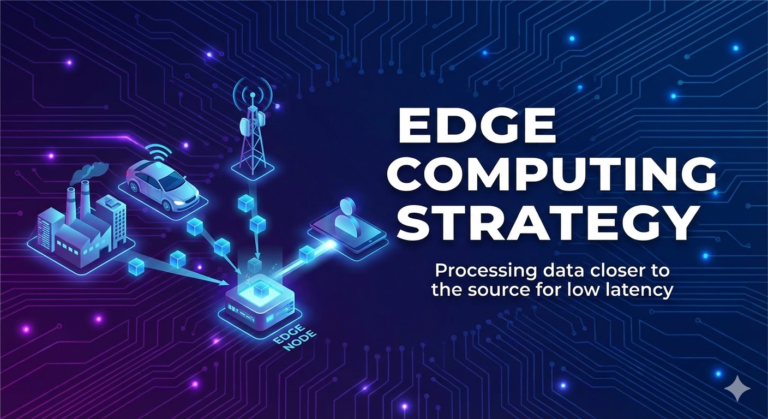
Edge Computing Strategy: Processing data closer to the source for low latency
In today’s hyper-connected digital world, speed is everything. Whether it’s a smart factory detecting equipment failure, a retail store analyzing…
Direct-to-Consumer (DTC) Tech Stacks: Optimizing IT for modern retail brands
The retail landscape has undergone a dramatic transformation over the past decade. Traditional retail models that relied heavily on distributors,…
Digital Sovereignty: Ensuring a business owns its data, not the software vendor
In the race toward digital transformation, businesses have rapidly adopted cloud platforms, SaaS applications, and third-party digital services to improve…
Digital Forensics in Consulting: Helping Businesses Recover and Investigate After a Breach
No organization plans to experience a cyber breach. Yet in today’s threat landscape, incidents are no longer a matter of…
DevSecOps Integration: Embedding Security into the Software Development Lifecycle
Speed has become the currency of modern software development. Organizations race to deliver new features, deploy updates weekly (or daily),…
Data Liquidity Strategy: Ensuring data flows freely between silos for better insights
In today’s digital enterprise, data is often described as the new oil. But unlike oil, data does not automatically create…
Data Gravity & Migration: Managing the challenges of moving massive datasets
In the early days of digital transformation, moving data was relatively simple. Databases were smaller, applications were fewer, and infrastructure…
Cyber Insurance Readiness: How consultants help firms qualify for lower premiums
Cyber insurance has shifted from a “nice-to-have” safeguard to a business necessity. With ransomware attacks, data breaches, and supply chain…